Science & Technology

Hundreds of government websites, including the Department of Immigration, were inaccessible on Saturday due to a cyberattack on the government servers.
The attack affected as many as 400 government websites, according to the National Information Technology Center (NITC), responsible for the Government Integrated Data Center (GIDC) operation. Many of them have since been restored.
The Department of Immigration bore the brunt, as the operations at the Tribhuvan International Airport ground to a halt for several hours. Hundreds of passengers of six international flights were stranded as the airport authorities failed to carry out immigration procedures.
A preliminary investigation by the NITC points to a type of attack called a Distributed Denial of Service (DDoS).
What is it, and how were the servers taken offline?
DDoS
In this kind of attack, IT experts say, the main goal is not to hack into the servers and get to the data. Instead, as the name suggests, the goal is to stop the service or freeze the websites to stop the service.
The server has a certain amount of space to process the query – the number of clicks or visits to the website. If the space runs out, the server cannot handle any more requests.
Such attacks are not exclusive to servers in Nepal and often happen to sites all across the world.
"The attack penetrated the system as our infrastructure was incapable to repel it because of the little throughput," said Ramesh Prasad Pokhrel, assistant director and information officer at the NITC.
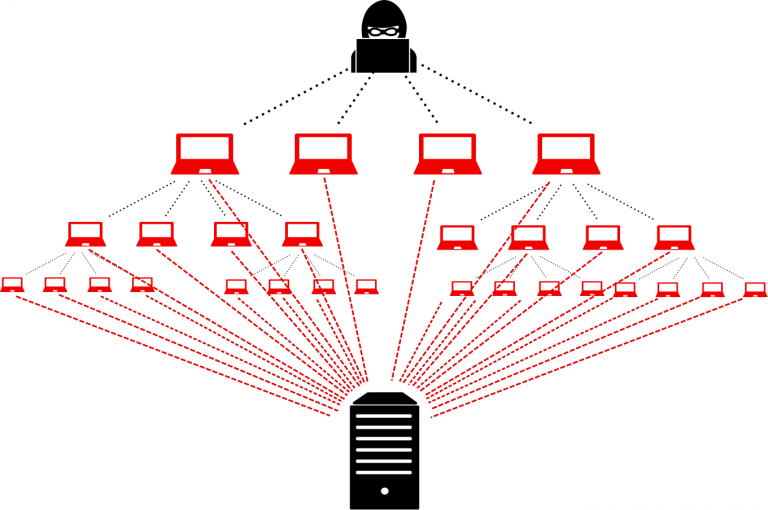
In a distributed DoS, more than one computer on more than one network sends repeated requests, overloading the server.
Attackers can use what they call a ‘botnet’. A botnet is a network of computers that are spread out all over the world and have been hacked by viruses and other malicious programs. Without the user's knowledge, the computers that have been hacked form a network of computers that send requests to the servers on behalf of the hackers.
Meanwhile also read: Nepal Police calms fears over escalating AI-based cybercrimes
This amplifies the power and complexity of an attack and in Nepal’s case, this is the most likely scenario, according to officials, a preliminary analysis suggests.
Pokhrel said: “We have started an investigation. We can ascertain the type and complexity of attack after a report. But one thing is sure: because it was a distributed DoS, our system had a hard time stopping the attack.”
Workarounds and prevention
The system was inaccessible for more than two hours on Saturday afternoon and had multiple outages throughout the day, however, as the officials claimed, no data has been leaked in the attack.
According to Pokhrel, the system continues to experience such attacks, but as a simple remedy, the experts at GIDC have barred access to the server from foreign soil. “This has brought the request within the capacity of the Nepali server architecture,” he said.
The throughput of the data centre is 15 Gbps (Gigabits per second) which is very low compared to the size of DDoS attacks. The average DDoS attack power was 9.15 Gbps in the first quarter of 2021. And the largest reported DDoS attack was tried on Google in 2017 with a power of 2.54 Tbps (terabits per second) in which attackers tricked even servers into becoming a part of their botnet.
In the absence of a robust firewall, servers in Nepal will likely be subjected to such attacks repeatedly, Pokhrel warned, calling for a robust mechanism to identify and block such attacks.
“Meanwhile, we are also working on multiple solutions to avoid such attacks,” he said.
Pokhrel also mentioned the possibility of creating a stand-alone system in which NITC would divide the network into sections that would essentially operate as independent servers for specific websites or services.

“We are trying to deploy such a system for very important services like for the immigration department. It will work as an intranet – meaning it is a standalone system that can even function without the internet,” he added.
As it originated from a distributed network, the system at GIDC was initially unable to filter the IP address of the attacker because it was difficult to determine which IPs among thousands were participating in the attack.
Technicians are trying to switch resources to trick the attackers, according to the NITC officials. “To put it simply, hackers are apparently attacking the system in one way,” Pokhrel said. “Stopping the flood of query requests will be easier if a whole new way is made and traffic is redirected.”
Also read: Nepal Police calms fears over escalating AI-based cybercrimes
Also read: Five ways to protect your social media accounts from snooping hackers
Also read: Social media addiction among Nepali children adds to security and health worries






